Trust: the Price of Admission in the Agent Ecosystem
The hard problem isn’t building smarter agents; rather, if we are going to have hundreds, thousands, or maybe millions of agents in each enterprise, then it’s about building the social infrastructure for trust at-scale; it’s about making the entire agent ecosystem and the agents in them transparent, auditable, certifiable – and trusted.
Introduction
The agent story we have been selling ourselves is pretty darn compelling: software that can reason, coordinate, and execute work with the quiet precision of your smartest fellow worker. The promise is not just efficiency. It is agents that are always-on, always listening, and always working. But in practice, there is a gate every enterprise will eventually hit, and it is not model quality, intelligence, or even token costs. Rather, it is trust.
Trust is the price of admission in the agent ecosystem.
Today, most organizations still live in a familiar pattern: data flows in, analysts and systems derive insights, and then people decide what to do. The distance between insight and action is deliberately long, routed through meetings, approvals, second opinions, and the quiet friction of accountability. That friction is not a bug; it is the mechanism that keeps intent from becoming irreversible execution without scrutiny.
Tomorrow, agents collapse that distance. They will not just analyze data and surface recommendations; they will take action - calling APIs, triggering workflows, moving money, changing configurations, messaging customers, delegating work to other agents. The path from intent to execution becomes dramatically shorter, and therefore dramatically riskier. If an enterprise expects thousands - or eventually millions - of these actors operating continuously, trust can’t be something you infer from a good demo or a pilot that didn’t blow up. It has to be infrastructure: verifiable, auditable, and certifiable.
This article lays out Agentic Mesh’s seven-layer trust framework - best understood as a stack - from identity at the foundation to governance at the top. We walk through each layer and show how, together, they turn trust into something operational: purpose plus proof, trust in the ecosystem (not just the agent), and federated trust that can survive scale across teams, vendors, and organizations.
Trust Themes
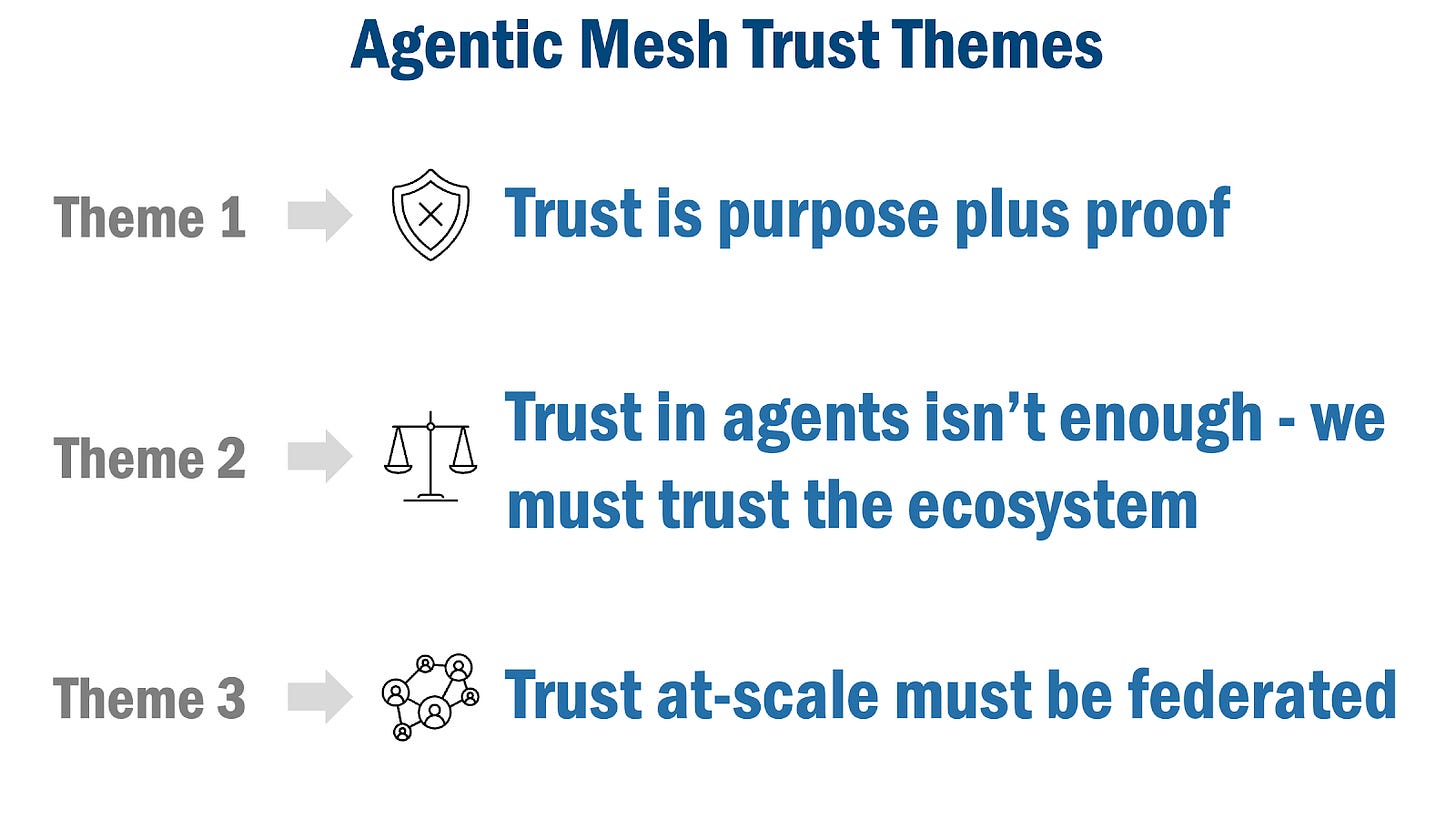
The argument of this article rests on three themes that reinforce one another. The first defines what it means to trust an agent in practical terms. The second raises the level of abstraction: trust cannot be limited to the agent, because agents only matter inside an ecosystem that must itself be trustworthy. The third addresses the inevitable reality of scale: if enterprises really deploy thousands or millions of agents, trust cannot be handcrafted or centralized - it has to be federated, repeatable, and portable.
Figure 1: Agentic Mesh Trust Themes
Theme #1: Trust is purpose plus proof
A trusted agent is one that fulfills a defined and transparent purpose and demonstrably adheres to its purpose and policies - no more and no less. That definition is intentionally narrower than “a capable agent,” because capability is not the same thing as reliability. In production, trust is not a feeling generated by a good conversation or a reassuring answer; it is the ability to point to concrete evidence that the agent stayed within bounds.
The emphasis on “demonstrably” changes how systems must be built. It pushes purpose and policy out of informal prompts and into durable declarations, tied to identity and enforced through controls. It pushes execution out of the shadows and into visibility - plans that can be inspected, permissions that can be verified and revoked, and traces that can be audited. In other words, purpose is the claim; proof is the mechanism that makes the claim believable at enterprise risk levels.
Theme #2: Trust in agents isn’t enough; we must trust the ecosystem
Even if you could certify that a single agent behaves correctly, that does not automatically make an enterprise comfortable deploying it at scale. Organizations do not run on individual trust alone. They rely on institutions - roles, supervision, escalation, audit, and accountability - because those structures make behavior legible and enforceable across large populations of people. The same is true for agents: they inherit both their power and their risk from the environment they operate in.
So “trust in the ecosystem” means believing the surrounding system is governed, and therefore capable of enforcing rules consistently. It means the ecosystem is transparent enough to understand what agents are supposed to do, observable enough to see what they are doing, explainable enough to justify why decisions were made, and auditable enough to reconstruct events when something goes wrong. Most importantly, it means accountability exists: someone owns the agent, someone owns the policies, and the system has mechanisms to quarantine, revoke, or retire an agent when trust is violated.
Theme #3: Trust at scale must be federated
The moment you move from a handful of agents to hundreds, thousands - or millions - the trust problem changes category. You cannot inspect everything manually, and you cannot rely on one central authority to vet every agent across every department, vendor, and jurisdiction. Trust has to become repeatable and portable: evidence that holds up when an agent crosses boundaries, and verification that does not depend on trusting the original builder.
This is where federation becomes the foundation rather than a nice-to-have. Industrial societies solved “trust at scale” long before software agents by building standards-based regimes: UL and CSA certify products through shared standards, accreditation (delegating authority to certify), and attestation (verifiable claims that travel with the product). The agent ecosystem needs the software equivalent - standards for identity, roles, policies, evidence, and certification - so trust can move across organizations without collapsing into bespoke negotiation. Federation is how you turn autonomy from a local experiment into infrastructure that can safely scale.
The Agentic Mesh Trust Framework
Soon we will see thousands - or even millions - of agents inside a single enterprise, as many industry leaders now predict. At that scale, the familiar safety blanket of “human-in-the-loop” stops being a control strategy and becomes a bottleneck: you can’t approve, review, or second-guess every action without erasing the very autonomy you deployed agents to achieve.
From a practical perspective the operating model probably needs to change. Humans move “above the loop” - defining purpose and policy up front, supervising through evidence, and stepping in only when the system flags uncertainty, exception, or drift. But that shift only works if trust stops being a sense or feeling you get from a good demo and becomes a capability you can verify. In production, trust is the price of admission to the enterprise agent ecosystem.
So, it is probably not very surprising that the conversation about agents keeps coming back to the same question: what does it mean to trust an agent? For people, trust is often social and intuitive. We read tone. We infer intent. We intuitively understand credibility. We grant trust gradually, with context, reputation, and norms acting as scaffolding. Organizations make this workable because they surround people with structure: roles, supervision, escalation paths, audit trails, and consequences. Trust is never just a judgment about a person; it is also a judgment about the institution behind them.
Agents are different. If you are a ChatGPT user (with 800 million weekly users, you probably are) then you know that agents (and large language models) can be capable without being very accountable, helpful without being terribly constrained, and persuasive while sometimes being wrong. And they operate at machine speed - meaning a small lapse becomes a large incident quickly.
A trusted agent, then, must be something more specific than a “good” or “smart” agent: it is one that fulfills a defined and transparent purpose and demonstrably adheres to its purpose and policies - no more and no less. The key word is demonstrably. In an enterprise context, trust is evidence, produced by systems that are transparent, observable, explainable, and auditable.
That is why trust becomes an ecosystem problem the moment you aim for scale. If enterprises are going to run thousands, or even millions, of agents, trust can’t be hand-crafted or bespoke and it definitely can’t be centralized. It must be repeatable, portable, and federated.
Building a trust ecosystem at that scale is hard - but it is not unprecedented: in the physical world, organizations like Underwriters Laboratories have already built federated systems that let millions of products be trusted without being personally re-checked every time they change hands. In fact, Underwriters Laboratories began as a practical response to a new kind of danger: electricity spreading into American buildings faster than anyone could confidently say it was safe. Fire insurers weren’t chasing philosophical certainty; they were trying to stop losses in a world where a bad wire, a cheap insulator, or a poorly built device could turn a building into fire hazards. UL’s insight was not “we will inspect everything forever,” but “we will make safety legible” using test methods, published standards, certification marks, and a system of evaluation that could travel with a product from factory to job site to insurer’s ledger.
Agents need the software equivalent of the UL trust ecosystem - not a one-time security review or a heroic central team that “knows” which agents are safe, but a trust approach that scales with adoption and survives vendor boundaries. In practice that means shared, checkable artifacts: identity and provenance that can be verified automatically; declared capabilities and policy constraints that are machine-readable; standardized evaluations for behavior, safety, and reliability; and attestations that can be issued, audited, and revoked as models and tools change. The point of our UL analogy is that trust becomes a property of the system, not the personality of the product. When an agent moves across teams, vendors, and organizations, its trust should move with it - carried by certifications, logs, and enforceable contracts the way a safety listing travels with a device - so the agent ecosystem can adopt quickly without pretending the risks are gone.
Agentic Mesh’s Trust Framework provides that structure. It is a seven-layer model - best understood as a stack - that builds from identity at the foundation to governance at the top, separating concerns so trust can be engineered, verified, and certified. The first layers establish who an agent is and what it is allowed to do; the middle layers make behavior explainable and observable; and the top layers make trust portable across ecosystems through certification and governance. In the sections that follow, we walk through each layer and show how the stack, taken together, makes trust at scale possible.
Figure 2: Agentic Mesh Trust Framework
Layer 1: Identity and Authentication
Every trust system begins with a basic premise: you cannot trust what you cannot identify.
In human life, identity is so routine we forget how much it carries. A passport, a driver’s license, an employee badge - these aren’t status symbols. Instead, they are anchors for accountability. They let a system say, with confidence, this is who you are, which is what makes it possible to decide what you’re allowed to do, what responsibilities you carry, and what happens if you violate expectations.
Agents need the same anchor. If an agent is merely “some process running somewhere,” every higher control becomes fragile. Authorization becomes guesswork. Audit trails become questionable. Blame becomes diffuse. And in a multi-party ecosystem, impersonation becomes cheap. You can’t build serious oversight on top of a participant whose identity is fuzzy.
So, identity for agents must be verifiable, not declarative. In practice that means cryptographic identity: keys, certificates, signed assertions, and mutual authentication between parties. Mutual TLS is the simplest intuitive model - the agent proves itself to the service, and the service proves itself to the agent - so both sides can confirm they’re talking to who they think they’re talking to. That isn’t a fancy feature; it’s the starting line.
Identity is also lifecycle. For people, identity documents expire, get renewed, and can be revoked. In a serious system, agents need the same discipline: keys rotate, certificates expire, compromised credentials are revoked, and decommissioned agents lose the ability to authenticate. This matters because agents are not static. They get replicated, scaled up and down, rebuilt, and redeployed. Identity has to be stable without becoming sloppy - or worse, permanent.
This is where the definition of trust stops being abstract and becomes operational: trust is purpose plus proof, and identity is the “who” attached to the proof (Theme 1). Without identity, you don’t have the basic foundation for trust.
And identity is also where trust at scale starts to become real. In a world of millions of agents, you won’t have one global registry that everyone uses; we expect to see multiple trust domains - enterprises, vendors, clouds, consortiums - each with their own identity roots. The obvious challenge is to make it interoperable and governed, so identity can be verified across boundaries without collapsing into one-off exceptions (Theme 3).
Layer 2: Authorization and Access Control
Once you can reliably say who an agent is, the next question is plain: what is it allowed to do?
For people, we accept authorization systems as normal. Job roles. Department boundaries. Approvals. Separation of duties. You can be trusted as a person and still not be trusted with payroll. That is not an insult. That is governance.
Agents require a stricter version of the same logic, because agents can act at machine speed, and their mistakes can propagate faster than a human can intervene. The default posture must be zero trust: never trust, always verify.
In practical terms, authorization is how purpose becomes enforceable. It is the guardrail that turns “this agent is supposed to do X” into “this agent can only do the actions required to do X.” Tokens with scopes. Role-based and attribute-based access control. Policy decision points that evaluate context. These are implementation choices, but the underlying principle is constant: least privilege, continuously verified.
Just as important, authorization should often be short-lived by design. In many workflows, the safest permission is not a standing entitlement but a narrow, time-bound grant: a token that expires quickly, a one-time approval to execute a specific step, or a scoped credential that is valid only for the duration of a task. This is how you prevent permission drift - where agents quietly accumulate access because it was convenient - and how you keep autonomy from turning into permanent privilege.
It is tempting to give agents broad access “so they can be helpful.” That temptation is the fastest route to incidents. Helpful is not the goal. Governable is the goal. Agents should begin in a sandboxed state with minimal permissions and must earn additional scope through explicit grants that are justified by their role and purpose - and, where possible, those grants should be temporary and revocable without drama.
This is one of the cleanest places where “trust is purpose plus proof” becomes concrete: authorization is part of the proof (Theme 1). If an agent cannot access what it is not allowed to access, then policy violations shrink from catastrophic to inconvenient.
And it’s also where you see why trusting the agent is never enough. Access control is a property of the ecosystem, not the agent alone (Theme 2). The strongest intentions are meaningless if the surrounding system cannot enforce permissions. In human organizations, policies are only real when they can be enforced - by managers, auditors, or systems. In agent ecosystems, enforcement has to be automated, consistent, and logged.
Layer 3: Purpose and Policies
Identity tells you who the agent is. Authorization tells you what it can do. Purpose and policies tell you what it is supposed to do - and what it must never do - even if it technically could.
This layer is often misunderstood because it sounds like documentation. It is not. Purpose and policies are the agent’s charter: the terms under which the ecosystem agrees to let the agent exist, and the benchmark the ecosystem will later use to judge whether the agent stayed in bounds.
For people, we separate capability from responsibility all the time. A person may be capable of making a decision, but policy may require escalation. A person may have access to information, but policy may forbid using it in certain contexts. A person may be authorized to spend money, but policy may require two signatures above a threshold. These are governance constructs that can’t be reduced to “permissions,” because they’re really about intent, accountability, and acceptable behavior - not just access.
Agents need the same structure, but more explicit. Their purpose should be stated plainly and operationally, in language humans can review and machines can apply. Not “improve customer experience,” but “draft customer support responses using approved knowledge base articles; never send directly to customers; flag uncertain answers for review.” When purpose is vague, trust collapses into interpretation. When purpose is clear, trust becomes testable.
Policies are the constraints that operationalize that purpose. They define boundaries around truthfulness (“do not invent facts”), action (“do not execute transactions without approval”), data (“never store raw PII”), and behavior (“do not attempt to bypass access controls”). The crucial move is that these policies are explicit and durable. They are not hidden in prompts. They are not informal conventions. They are part of what the ecosystem can audit, enforce, and ultimately certify.
This is the spine of “trust is purpose plus proof” (Theme 1). Purpose and policy are the claim; everything else in the stack exists to make adherence demonstrable - so violations can be detected, explained, and acted on, rather than argued about after the fact.
And this layer quietly determines whether trust can scale. If agents from different organizations are going to collaborate, purpose and policy declarations can’t be private dialects; they need standardized shapes and shared vocabularies (Theme 3). In a federated world, interoperability isn’t just about APIs - it’s about common expectations that can be verified across boundaries without constant negotiation.
Layer 4: Task Planning and Explainability
An agent can be authenticated, scoped, and policy-bound - and still behave in ways that make enterprises nervous. The missing piece is often not control but understanding.
Layer 4 is where the black box begins to open. Not by exposing every internal thought, but by making the agent’s work legible: what plan it formed, what steps it intended to take, what tools it chose, what data it relied on, what assumptions it made, and what it did when uncertainty appeared.
In human organizations, explainability is an expectation, not a luxury. A junior analyst can’t just deliver a number; they have to explain where it came from. A manager can’t just say “do it”; they have to justify the decision when asked. Explainability is how accountability becomes practical, because accountability requires reasons, not just outcomes.
Agents need an analogous standard. A plan is a contract with the future. It lets operators see what the agent is about to do before it does it, and it lets auditors reconstruct what it intended to do after the fact. Just as importantly, it creates a natural surface for enforcement: “This step violates policy X,” “This tool requires additional authorization,” “This action should be escalated,” or “This output needs human review.”
This is also where trust becomes safer in a subtle way: explainability reduces surprises. Surprises are what kill adoption. Enterprises will tolerate occasional errors; they will not tolerate opaque errors that cannot be explained, reproduced, or bounded. When an agent can show its plan and rationale, failures become diagnosable events instead of unsettling mysteries.
This is the point where trusting the agent as a standalone actor clearly isn’t enough. You also have to trust the system around it - the ecosystem that records plans, enforces gates, and makes decisions reviewable (Theme 2). If the ecosystem cannot explain why an agent did what it did, governance becomes theatre: rules exist on paper, but accountability collapses in practice.
And at scale, explainability stops being just transparency and becomes coordination. In multi-agent workflows, plans are how agents align expectations, avoid duplicate work, and hand off tasks without improvising themselves into conflict. Planning is not just how an agent “shows its work”; it is the social order that makes large fleets of agents manageable (Theme 3).
Layer 5: Observability and Traceability
Layer 4 is about what the agent says it will do and why. Layer 5 is about what it actually did, when, and in relation to everything else.
Trust is not sustained by intentions. It is sustained by evidence.
Observability is the discipline of instrumenting a system so its behavior can be monitored and understood. Traceability is the discipline of connecting events into coherent narratives: this action belonged to this task, which was triggered by this request, which delegated to these agents, which invoked these tools, which produced these artifacts. Without that connective tissue, you don’t have a system you can manage - you have activity you can’t explain.
In an agent ecosystem, traceability is not optional. Agents work asynchronously. They delegate. They retry. They communicate and collaborate across boundaries. Without strong correlation identifiers - task IDs, conversation IDs, step IDs - you get a fog of logs that cannot tell a story. And if you can’t tell the story, you can’t debug. You can’t audit. You can’t certify. The difference between a minor incident and an existential loss of confidence is often nothing more than whether you can reconstruct what happened.
For people, organizations create traceability naturally: email threads, ticketing systems, approvals, meeting notes, audit logs, and records management systems. Those artifacts are sometimes messy, but they exist. For agents, we have to build traceability deliberately, because the system will otherwise move too fast to reconstruct - and because agents don’t leave “paper trails” unless the ecosystem forces them to.
This is where “purpose plus proof” stops being rhetoric and becomes operational (Theme 1). Demonstration requires records, and records require observability. If you can’t show what an agent did, you can’t claim it behaved - even if the outcome looked fine.
This is also where trust in the ecosystem becomes tangible. Trusting the ecosystem means trusting that it captures reality faithfully: tamper-resistant logs, consistent schemas, clear retention, and the ability to reconstruct events under pressure during incident response (Theme 2). It’s the difference between “we think the agent behaved” and “we can prove the agent behaved.”
And at scale, observability is how trust stays alive over time. Drift happens. Policies evolve. Threats change. Without monitoring, you don’t notice drift until it becomes a breach. Observability turns trust into a living discipline - continuously assessed, continuously reinforced - which is the only version of trust that survives large fleets of agents operating across organizations (Theme 3).
Layer 6: Certification and Compliance
Now we reach the point where the trust stack stops being purely internal and becomes an external signal.
Enterprises do not only want to know that they have controls. They want to know those controls have been evaluated against a standard, in a repeatable way, with evidence. That is certification: not a claim of safety, but a structured basis for believing it.
This is where Underwriters Laboratories and the Canadian Standards Association stop being metaphors and start being models. UL and CSA scaled trust by creating standards and processes that could be applied across millions of products. They did not personally inspect every toaster forever. They created a system of standards, accredited labs, and certification marks backed by auditing and enforcement. That is federation in action: trust is defined centrally in principle but is executed in a distributed fashion in practice.
Agent ecosystems need the same structure.
Certification for agents means structured evaluation against declared purpose, policies, and operational constraints. You test the agent under expected conditions and adversarial conditions. You verify it stays within authorization bounds. You inspect trace data. You review whether its planning and explainability meet required thresholds. You assess resilience: how it behaves when it cannot access required resources, when prompts are ambiguous, when data is missing, when policies conflict. Certification turns “we think it’s safe” into “we have evidence it behaves within its contract.”
Compliance is the bridge between technical control and organizational obligation. Enterprises are governed by laws, regulations, and internal policies - privacy rules, financial controls, safety standards, industry constraints. Certification becomes meaningful when it can be tied to those obligations in plain terms: “This agent is certified to handle this class of data,” “This agent is certified for this regulated workflow,” or “This agent is not certified to operate without human approval.” That is what makes certification actionable in procurement, deployment, and audit.
This is the layer where federated trust becomes unavoidable (Theme 3). If you want thousands - eventually millions - of agents, you cannot have one committee certifying every agent by hand. You need standards. You need accredited certifiers: delegated groups that can certify within defined scopes. And you need attestation: machine-readable evidence that the agent is certified, by whom, for what, and until when - so other systems can verify trust without personal relationships.
Finally, certification cannot be a one-time sticker. Agents evolve: they gain tools, change prompts, update models, shift configurations. Certification has to be version-aware and event-driven. Significant changes trigger recertification. Violations trigger suspension or revocation. In the physical world we call this recalls; in agent ecosystems, it is simply the minimum discipline required to keep trust intact once autonomy is deployed.
Layer 7: Governance and Lifecycle Management
If certification is the trust signal, governance is the trust engine that keeps the signal meaningful over time.
This layer answers the question that most enterprises are really asking, even when they phrase it differently: who is accountable?
In human organizations, trust depends on governance structures: managers, compliance officers, audit committees, regulatory frameworks, and processes for escalation and discipline. People may be competent, but the organization is trusted because it can detect problems, respond to incidents, enforce standards, and improve itself over time. The institution is what turns individual competence into something society is willing to rely on.
Agent ecosystems require the same institutional backbone. Governance defines the rules and the mechanisms for enforcing them. It defines ownership - every agent must have an accountable owner. It defines change control - what kinds of modifications require review and recertification. It defines incident response - how to quarantine an agent, revoke credentials, roll back access, and investigate behavior. And it defines lifecycle - how agents are onboarded, operated, updated, recertified, and retired - so that trust survives contact with reality and time.
This is where trust in the ecosystem gets its fullest meaning. Trust in an organization - or in an agent ecosystem - is not the belief that participants are well-intentioned; it’s the belief that the system is governed under applicable rules and laws, that its controls are transparent, that behavior is auditable, that accountability is enforceable, and that the ecosystem can correct itself when it fails (Theme 2). Without that machinery, “trust” becomes a marketing word, because there is no credible consequence for violating it.
Governance is also where federation stops being theory and becomes operating practice. In a multi-party ecosystem, there is no single sovereign authority. You may have consortium standards. You may have regulatory overlays. You may have mutual recognition agreements - “we recognize certifications issued by these accredited bodies under these conditions” - that let trust cross organizational borders without collapsing into one-off negotiations (Theme 3). This is how industrial trust scales. It is how international trade functions. It is how the web works. And it is how large-scale agent ecosystems will have to work.
Lifecycle management matters because trust is most vulnerable at transitions. Onboarding is where misconfigurations slip in. Updates are where drift enters. Decommissioning is where zombie agents appear - credentials that still work after the agent is supposedly gone. A governed lifecycle makes trust durable by ensuring that identity, access, observability, certification, and accountability survive change, not just steady state.
Conclusion
The agent future will not be decided by model quality, “intelligence,” cost, or speed alone. It will be decided by whether enterprises can justify trust - first in individual agents, and then in the ecosystems those agents run in. That is what Agentic Mesh’s seven-layer trust framework is really doing: turning trust from a sentiment into a framework, or stack, built from identity at the bottom to governance at the top, so agents can be deployed with confidence.
At the agent level, the standard is simple and unforgiving: trust is purpose plus proof (Theme 1). A trusted agent is not one that sounds smart; it is one that fulfills a defined and transparent purpose and demonstrably adheres to its purpose and policies - no more and no less. “Demonstrably” means identity that can be verified, access that is scoped and often short-lived, behavior that is explainable through plans and rationale, and actions that are observable and traceable through auditable records.
But even perfect agent-level controls won’t carry the day if the surrounding system cannot be trusted (Theme 2). Enterprises rely on aviation, finance, and healthcare not because every participant is flawless, but because the ecosystems are governed: transparent enough to inspect, observable enough to monitor, auditable enough to reconstruct, and accountable enough to correct.
And because scale is the point, trust cannot remain bespoke or centralized (Theme 3). If we truly expect millions of agents across teams, vendors, and jurisdictions, trust at scale must be federated - standards, accredited certifiers, and machine-verifiable attestations that travel across boundaries, the way UL and CSA made safety legible across industrial supply chains. Without that scaffolding, the agent ecosystem stays a risk story; with it, the agent ecosystem becomes powerful and reliable infrastructure.
***
This article was written in collaboration with John Miller. Feel free to reach out and connect with the authors - Eric Broda and John Miller on LinkedIn. Questions and comments are welcome and encouraged!
Looking for more?
👉 Discover the full O’Reilly Agentic Mesh book by Eric Broda and Davis Broda
🎧 Follow co-hosts John Miller and Eric Broda on The Agentic Mesh Podcast on Youtube, Spotify and Apple Podcasts. A new video every week!
***
This is part of larger article that addresses a broader suite of topics related to agents (see my full article list). If you like this article, you may wish to checkout an upcoming book, “Agentic Mesh”, with O’Reilly, and soon on Amazon.
***
All images in this document except where otherwise noted have been created by Eric Broda. All icons used in the images are stock PowerPoint icons and/or are free from copyrights.
The opinions expressed in this article are that of the authors alone and do not necessarily reflect the views of our clients.





Great read, Eric. The seven-layer stack is a rigorous and much-needed piece of infrastructure thinking for the agent era.
One question that sits at the intersection of Layer 7 and the learning challenge: most of the framework describes technical and procedural controls that can be engineered, verified, and audited. Where do you see the organization's learning capability living in the stack? Governance and Lifecycle Management defines ownership and processes, but the harder problem may be whether the humans at that layer can actually learn from the mesh over time, reading patterns in agent behaviour, not just detecting explicit policy violations.
Related to Layer 6: you describe certification as version-aware and event-triggered, which fits well for discrete changes in code, models, or policies. Curious how you think about the slower, behavioural kind of drift, where operational telemetry gradually reveals that a certified agent's effective behaviour no longer quite matches its declared purpose, not through a single update, but through accumulated interactions, data shifts, or emergent strategies.
I suspect there is a rich essay or two hiding in that space, and would love to see you tackle it.